Identify all data assets, locations, owners, and access paths across the organization.
Classify data based on sensitivity, impact, and regulatory requirements.
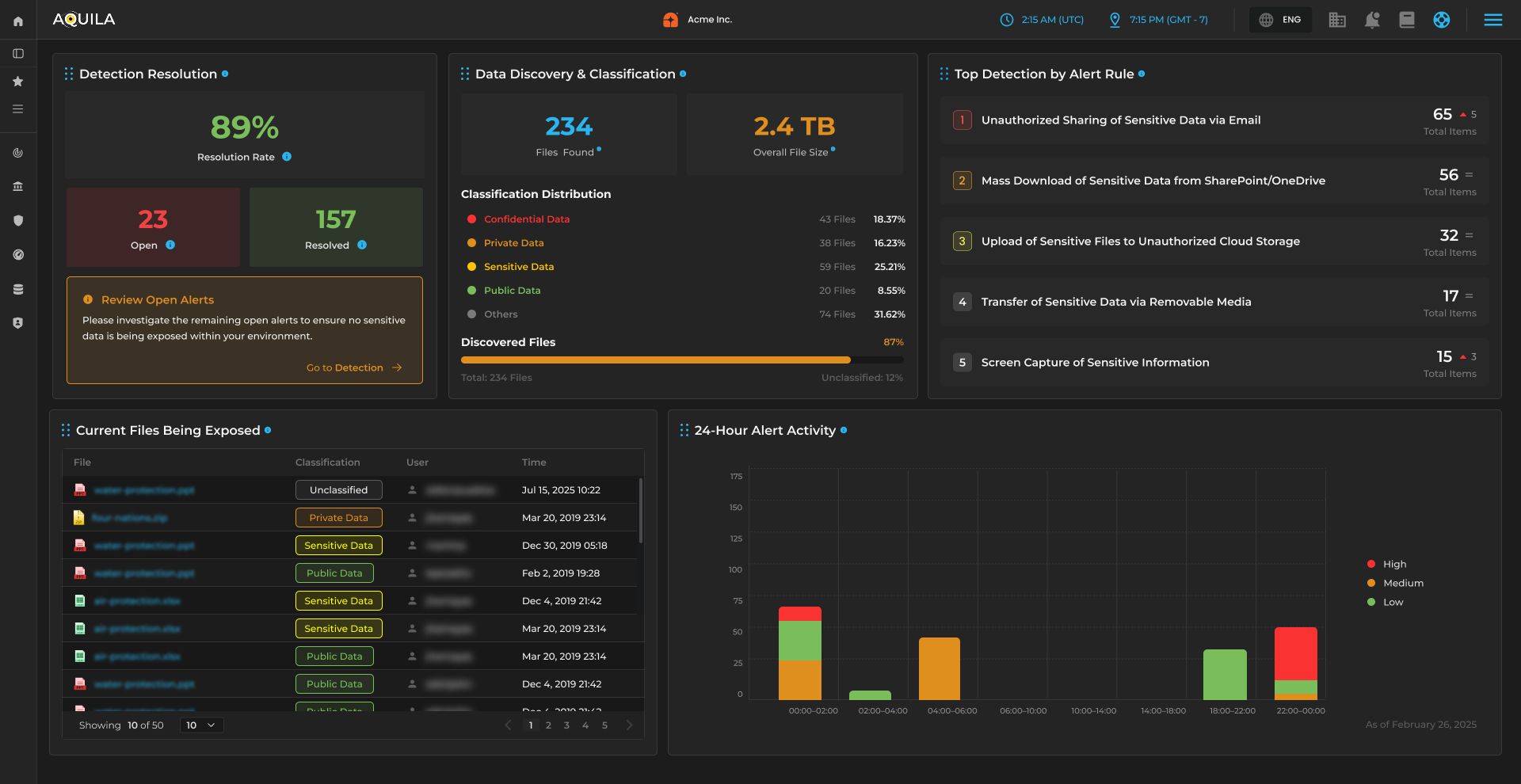
Monitor risks, misconfigurations, access exposure, and data movement in real time.
Build and maintain a long‑term, prioritized data security plan aligned with business drivers.

Most organizations don’t suffer data breaches because of weak encryption or missing tools — they suffer because they don’t know where their data lives, who has access, or how it moves. CyTech Data Security fixes this by combining discovery, classification, posture management, and governance into one unified system. It aligns technical controls with business drivers, regulatory obligations, and real‑world data usage, giving CISOs a complete, actionable view of their data environment.

Traditional tools focus on isolated controls. CyTech unifies discovery, classification, posture management, and governance into one C4I‑aligned system.
Data Discovery, Data Classification, Data Security Methodologies, Data Security Posture Management, and the Data Security Roadmap.
It identifies all data assets, locations, access paths, and owners — providing a complete map of the organization’s data landscape.
It ensures data is protected based on sensitivity, business impact, and regulatory requirements — enabling proper controls and governance.
DSPM continuously monitors data risks, access exposure, misconfigurations, and compliance gaps across all environments.
Organizations typically reduce data exposure by 40–70%, cut compliance effort by 35–60%, and eliminate 50–80% of manual data governance work — resulting in $300K–$2.4M in annual savings depending on environment size.