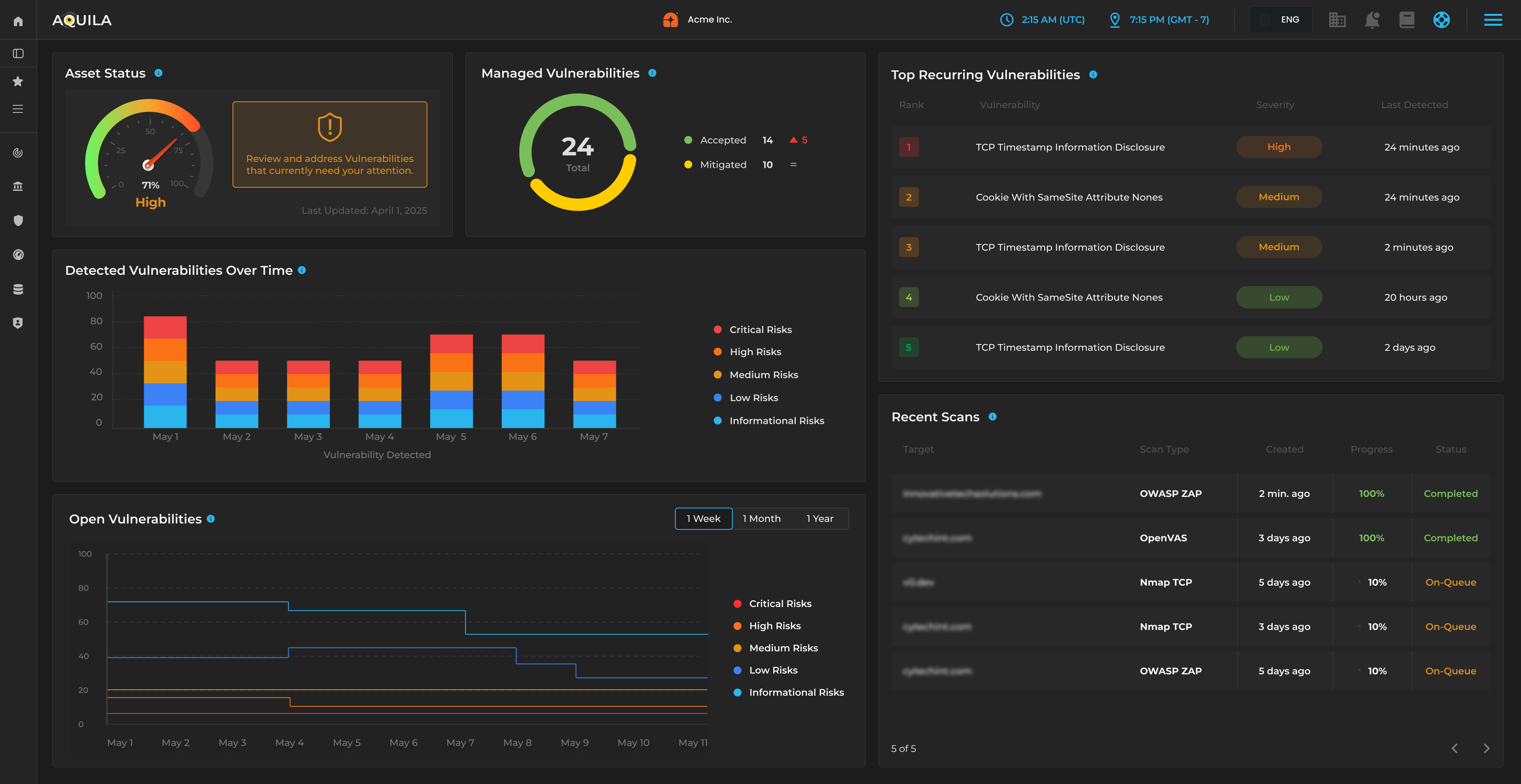
AQUILA Endpoint Agent integrates a real‑time VDR capability that detects vulnerabilities directly on the endpoint, guides mitigation workflows, and synchronizes remediation outcomes with AQUILA C4I’s central intelligence layer.


![[interface] image of a computer showcasing educational software (for a edtech)](https://cdn.prod.website-files.com/6954708495d04649d41c9ddd/69adb3737f932ac648f280fb_VDR%204.jpeg)

Traditional vulnerability management relies on periodic scans, network‑based discovery, external scanners with limited endpoint context, delayed reporting cycles, and manual remediation workflows.
This creates a structural gap:
• Vulnerabilities are discovered late
• Remediation is disconnected from detection
• Endpoint context is missing
• SOC and IT teams operate in separate workflows
• Risk decisions lack real‑time visibility
AQUILA Endpoint Agent corrects this by embedding VDR directly into the endpoint architecture, eliminating the delay between discovery, prioritization, and remediation.

AQUILA’s VDR module operates locally on the device, enabling:
• Real‑time detection of known and emerging vulnerabilities
• Continuous monitoring of software, configurations, and packages
• Endpoint‑level visibility into exposure, not just network‑level scans
• Contextual understanding of user behavior, processes, and system state
• Immediate reporting to AQUILA C4I Core OS
This ensures that vulnerabilities are identified as they appear, not during scheduled scans.

AQUILA VDR does more than detect vulnerabilities — it guides the remediation process.
When a vulnerability is identified, the agent:
1. Surfaces the issue locally
Users or IT teams receive clear, contextual prompts.
2. Guides mitigation
The agent provides step‑by‑step remediation workflows.
3. Tracks outcomes
AQUILA records whether the vulnerability was:
• Resolved
• Deferred
• Re‑opened
• Newly discovered
4. Reports back to AQUILA C4I
The central intelligence layer receives real‑time updates.
This creates a closed‑loop vulnerability lifecycle that traditional scanners cannot achieve.
AQUILA Endpoint Agent applies the C4I pillars directly to vulnerability management:
Command: Local enforcement of vulnerability policies, remediation requirements, and governance rules.
Control: Execution of automated or guided remediation actions at the device layer.
Communications: Continuous synchronization of vulnerability state with AQUILA C4I Core OS.
Computers: Local analysis of software versions, configurations, and exposure — even offline.
Intelligence: Correlation of vulnerabilities with behavioral signals, identity activity, and endpoint posture.
This alignment ensures that vulnerability detection is contextual, continuous, and operationally integrated.

AQUILA VDR shares the same telemetry engine as EDR, DLP, UEBA, AI‑driven monitoring, Local SOAR, Compliance enforcement, and Asset governance.
This allows VDR to evaluate vulnerabilities in the context of:
• Active processes
• User behavior
• Network activity
• Data access patterns
• Configuration drift
• Identity signals
Traditional scanners cannot provide this level of contextual risk interpretation.

AQUILA VDR continuously monitors:
Installed software, package versions, configuration states, missing patches, insecure settings, deprecated components, misconfigurations, and privilege exposures.
This enables the system to detect:
• Newly introduced vulnerabilities
• Unpatched software
• Insecure configurations
• Drift from baseline
• High‑risk combinations of exposure + behavior
Because VDR is integrated with EDR, UEBA, and AI‑driven monitoring, exposure is evaluated as part of the full attack surface, not as a standalone list.

AQUILA VDR supports guided remediation workflows, automated enforcement actions, user‑assisted mitigation, IT‑driven patching, configuration correction, and real‑time validation of fixes.
All actions execute locally, ensuring that remediation is:
• Immediate
• Verifiable
• Auditable
• Synchronized with AQUILA C4I
This reduces the time between detection and resolution dramatically.

With AQUILA VDR, organizations gain:
1. Real‑time visibility into endpoint vulnerabilities
No waiting for scheduled scans or external tools.
2. A unified vulnerability lifecycle
Detection, guidance, remediation, and validation — all in one system.
3. Contextual risk interpretation
Vulnerabilities are evaluated alongside behavior, identity, and system activity.
4. Faster remediation cycles
Guided workflows and local enforcement reduce delays.
5. A single source of truth for endpoint exposure
All vulnerability intelligence flows into AQUILA C4I Core OS.